This post is in partnership with Warner Bros. Pictures. All opinions are mine.

We love movies and I’m here with another movie coming to theaters soon! I’m so excited and am looking forward to seeing Wonder Woman when it hits theaters on June 2nd. I don’t know about you, but I wish I saw more movies with female superheroes and can’t wait to see a movie about the woman I grew up hearing so much about!

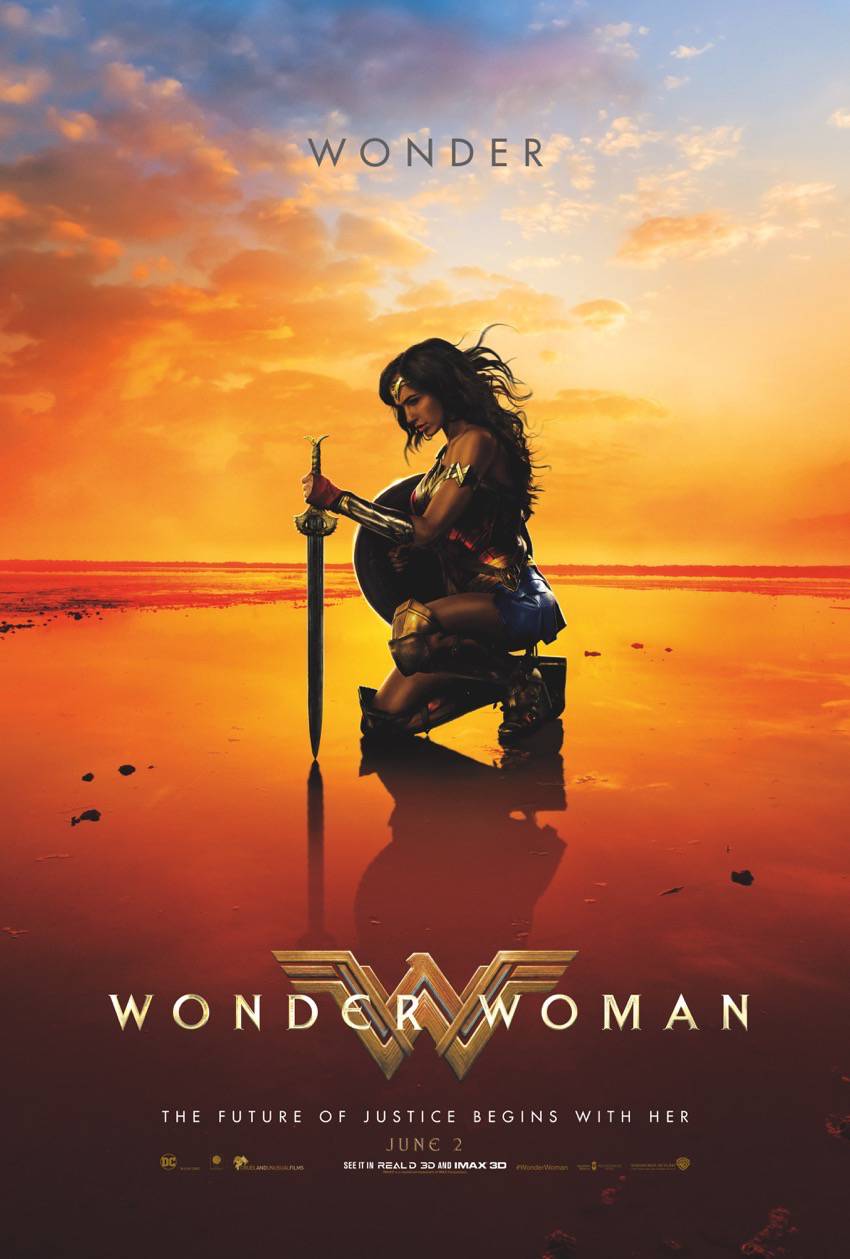
Power of a goddess. Heart of a hero. Gal Gadot is #WonderWoman, in theaters June 2.
From Warner Bros. Pictures and DC Entertainment comes the epic action adventure starring Gal Gadot, Chris Pine, Connie Nielsen and Robin Wright, directed by Patty Jenkins.

Before she was Wonder Woman, she was Diana, princess of the Amazons, trained to be an unconquerable warrior. Raised on a sheltered island paradise, when an American pilot crashes on their shores and tells of a massive conflict raging in the outside world, Diana leaves her home, convinced she can stop the threat. Fighting alongside man in a war to end all wars, Diana will discover her full powers…and her true destiny.

Wonder Woman Gauntlet Creator (Create Your Own Wonder Woman Image)
Power. Courage. Wonder.

Show us your warrior with the Wonder Woman gauntlet creator.
Check out Wonder Woman online and follow Wonder Woman on Twitter, Instagram and Facebook.
GIVEAWAY
One (1) lucky winner on The Mommy-Files will receive:
$50 Visa gift card to see the film in theaters
Open to US mailing addresses only. Prizing courtesy of Warner Bros. Pictures.
Who do you want to see Wonder Woman with?

I would see the movie with my sister.
I make sure to keep any lights off that don’t need to be on.
I want to see this movie with my sisters!
I save energy by turning off the lights, only using the clothes washer with a full load, taking less time in the shower, using low energy light bulbs.
I definitely want to see it with my daughter.
I would love to see Wonder Woman with my sister!
I use natural light as much as I can so I don’t have to turn lights on around the house in the day time.
I would love to take my daughter to see this. We tease and call her wonder Woman all the time because she is a fearless young lady always being the miss do gooder helping others.
My daughter and I are going!
My friend and I would be interested in going to see this one!
I would love to see Wonder woman with my husband. We are big Marvel fans.
I’d love to see Wonder Woman with my husband.
We have energy efficient appliances in our home to save energy.
I would like to see this movie with my husband and my daughter.
I would like to see Wonder Woman with my niece.
id like to go see it with my daughter that would be nice
I would watch it with my brother. He’s a fan and he’s watched all the episodes of the heroes. He’s a big fan of the Justice League.
I would love to see this with my fiance’.
I would take my friend to see it. He is a huge fan of Wonder Woman and I know he would like it.
I wash clothes in cold water and I just replaced my old a/c unit to a newer energy efficient model.
I would see this with my husband.
I would love to see this movie with my husband.
Thanks for the chance to win!
wildorchid985 at gmail dot com
I would like to see this with my daughters.
I would like to see ‘Wonder Woman’ with my sister.
I would see this with my son.
I’d like to see this with my daughter!
I used to love Wonder Woman on tv and would love to see the movie with my mom.
I would like to see this with my daughter.
I’d like to see this with my kids!
This looks so good. I would love to take my niece to go see this.
I would love to see Wonder Woman with a coworker.
I save energy by unplugging all the electronic devices that I am not currently using.
I would like to see it with my husband and kids. I think they would all enjoy it.
my tween grandkids
I’d love to go see it with my daughter!
I would like to see it with my sister.
I would love to see Wonder woman with my husband!
I would see this with my husband.
love to take my wife and my little niece
I would love to see this movie with my girlfriend.
I would take my mom to go watch Wonder Woman with me!
My husband will probably get a kick out of it.
Pingback: Wonder Woman is Coming to Theaters June 2nd + Giveaway!! | Your Family Stuff
This is going to be a movie I’ll see with the girls from our Senior’s lunch club.
I’d like to see this movie with my daughter.
Thank you!
My friend Mari is coming with me!
I would like to see this movie with my daughter.
I would take my friend to see this movie.
I want to see this with my daughters!
Would like to take my niece to this movie.
I would enjoy seeing Wonder Woman with my sis.
We were always big fans!
thank you
I save energy by unplugging things we do not use on a regular basis.
There is a noticeable savings!
I’d take my friend Lori.
I would like to see Wonder Woman with my husband.
I want to see Wonder Woman with my best friend.
My SIL Laura is a lifelong Wonder Woman fan, we are going opening day!
my husband
I would like to see Wonder Woman with my cousins.
I’d go with the bestie.
I would go with my daughter
I’d watch it with hubby! Totally can’t wait to watch this Wonder Woman movie together!
I’d go see it with my husband and kids
With my mom and grandmother!
all my friends
I’d like to see ‘Wonder Woman’ with my sweetheat.
We used to have doors closed, now we keep doors (bedroom, bathroom) open, the better air flow is better for your AC unit and it has driven our electric costs down.
my whole family it would be nice i saw some previews and it looks good by whole family my kids
I would love to take my family to see this or go for a girls night out!
I would see the movie with my bff.
I would like to see this with my best friend and a big tub of popcorn! 🙂
thanks!
I want to see it with my best friend.
I want to see it with my sister!
I would like to see Wonder Woman with my 24 and 11 year old sisters as well as my mom. They are my angels.
I would see this with my wife.
My youngest daughter
I’d see it with my sisters
I would go see the movie with my husband
any of the people i know, if theyre game i’ll go.
Believe it or not, my husband is excited to see Wonder Woman!
I would watch it with my mom
I’d have to go with my mom, she’s a huge fan!
With my sister!
I want to see it with my GF
I would like to see this with my best friend. Thanks for the chance to win!
I’d love to watch this film with my 23 yoa daughter. Thanks.
partymix25(at)hotmail(dot)com
I would like to see this movie with my daughter.
I would love to see it with my cousin Taylor.
I would see this movie with my mom and sister.
I’d like to see this movie with my husband.
I will go see it with my family
My whole family.
My niece would get a kick out of this movie.
Thanks for the contest.
I would like to see it with my husband
I love super hero movies.
I would like to see the movie with my nieces and nephew.
I would see this with my oldest daughter.
My 14 year old son we love going to the movies.
I’d see this with my husband
I’d love to see this with my daughter. 🙂
would love to see Wonder Woman with my friend
My niece thinks that she is wonder woman and I know she would love to see this.
I’ll probably have to tag along with some co-workers if I want to see the movie with someone because none of my friends want to see Wonder Woman.
I would like to see it with my daughter
I would like to see Wonder Woman with my husband and my grandchildren.
I’d love to see this with my sister!
I would like to take my fiance to go see this.
take my nephew
My hubby is a Wonder Woman fan. He WANTS to see this movie.
wow
I would like to see the movie with some friends.
I would love to take my Mom to go see Wonder Woman. Shes a huge fan plus its been a long time since we had a Mother-son day!
I’d see this movie with the kids.
I want to see this with my daughter, we can hardly wait!
I would see this with my husband.
I would love to see this with my mother.
I want to see it with my little nephew!
My niece Adrianna
I would love to go see this with my good friend.
I would definately love to see it with my hubby~
I would love to see it with my husband!
Want to see this in the big screen with my mom and sisters!
I want to see Wonder Woman with my son – he needs to understand that women can be as strong and powerful as they are beautiful!
I would see this movie with my wife
With my girlfriends…
I would see this with my dad. He loves superhero movies.
I would like to go see this with my friend.
My sister. Thanks.
I would like to see ‘Wonder Woman’ with daughter. Thanks for the giveaway!
I want to see this movie with my sis.
I would like to see it with my girlfriends.
Ill see it with my wife.
some friends of mine
Probably see it by myself in the movie theater with a huge tub of buttered popcorn. Which is always good company.
my spouse
My sister would love it
subscribe emails: slehan at myway dot com
I would like to see Wonder Woman with my niece.
I want to take the kids to see it.
I’d love to see this movie with my sister!
I would see the movie with a friend.
I would love to see Wonder Woman with my granddaughter!
I would love to see it with my husband.
I will see it with my husband.
I would love if my friend Janna could go with me to see Wonder Woman in theaters. She reminds me of a Wonder Woman with all she does and the same black hair style 🙂 & I’ll share my Red Vines!
I’d go with my family.
would love to see it with my sister
i would love to see it with my friend .ty 🙂
my niece
A friend.
I would see the movie with my daughter.
I would like to see Wonder Woman with my friend Betty who I also consider a Wonder Woman.
I would take my Daughter to see the movie.
Wonder woman is usually by herself. If I had to pick it would be Chris Evans.
I will go with my daughter
I would love to see it with my daughter
Wonder woman should date spiderman.
I would like to see Wonder Woman with my husband some date night.
I have a really good friend who would like to see this. She enjoys these types of films.
I plan on seeing this with my eldest niece.
I’d like to see it with a group of friends
I would see it with my husband.
i would like to take my daughter to see this
I would take my mom to see this!
I have plans to watch with my husband and another couple
I wanna see it with my husband! He actually wants to see it more than me 😊
I’d like to take my daughter to see the movie.
We use a programmable thermostat to reduce energy used by our A/C unit.
I would like to see this movie with my hubby.
I would like to see this with my hubby.
I would like to see Wonder Woman with my fiance
this is such the movie of the summer for me im going with my family
My daughter and I will attend the movie together
Would see it with my daughter.
I would like to see Wonder Woman with my sons.
This would be a good “dinner and a movie” night with my sisters.
I would go with my family!!
I would go to the movies and see it with my daughters.
I would take my boyfriend.
I would love to go see the movie with my nephew. He loves Wonder Woman too.
I want to see this with my husband!
I would like to see Wonder Woman with my mother.
I guess I’d see it with my mother.
I would like to see this with my daughter.
I would like to see it with my daughter.
I would like to see it with my daughters. Thank you!
I’d love to see Wonder Woman with my husband.
I want to see it with my daughter.
I’d take my daughter.
I would like to see this with my 10 year old granddaughter.
I would see the movie with my daughter.
I save energy by keeping doors sealed at the bottom, keeping the heating and cooling system clean and in good running order.
friends
My wife
I want to see it with my husband.
I would love to see it with my husband and kids.
I would see this with a friend from work. Thanks so much for the chances to win.
I would go with my husband
I would see this with my husband
I would go with my cousin. She is my movie pal.
I would most likely take my daughter.
i would like to see this with my daughter.
I would like to see this with my wife 🙂
I want to see the wonder woman movie with my husband. We are both big fans of wonder woman. We can’t wait!
With Hugh Jackman
I would love to see Wonder Woman with my daughter
I would love to see it with my husband.
I would love to see this with my husband
Great
I WANT TO SEE WONDER WOMAN WITH MY MAMA.
I’d see it with my daughter!
I would love to watch Wonder Woman with my daughter.
My wife & I are taking our daughters to see the new WW movie !!!
My husband
I would like to see it with my kids
I would like to see Wonder Woman with my granddaughter!
I’d like to see it with my family.
I’d see this with my cousin!
I would love to see this movie with my son
I would like to see this movie with my family.
I would like to watch this with my kids and hubby.
I’d probably see it with my wife. If not, then my neighbor.
I would love to see this with my grown daughter